The Decimation Cipher

Requires a Wolfram Notebook System
Interact on desktop, mobile and cloud with the free Wolfram Player or other Wolfram Language products.
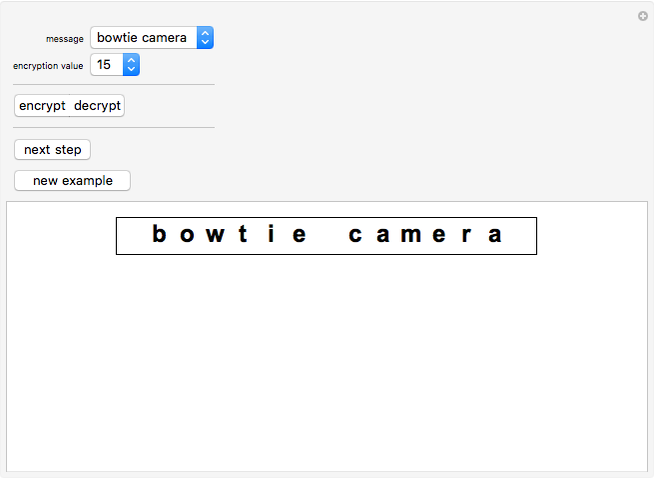
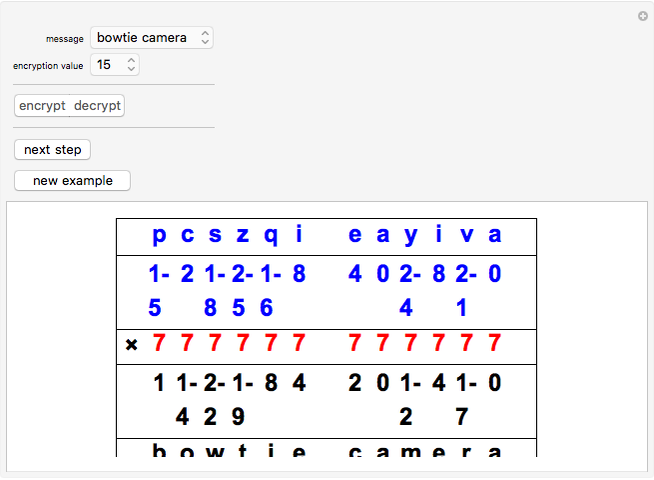
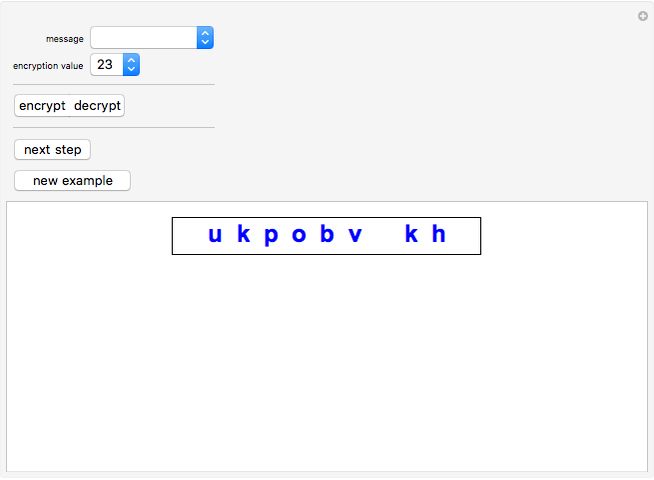
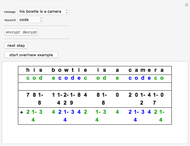
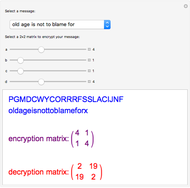
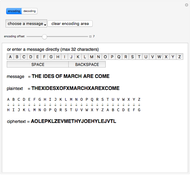
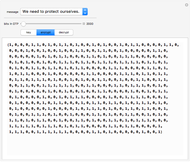
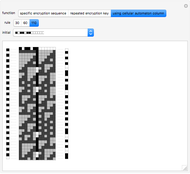
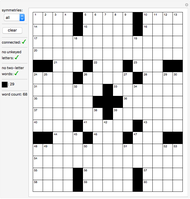
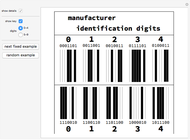
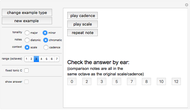
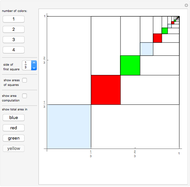
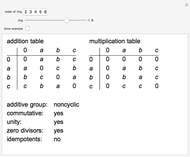
The decimation cipher encrypts a message by using modular arithmetic. Each letter in the message is replaced by its position in the alphabet (a → 0, b → 1, …, z → 25). These position values are then multiplied by an encryption value. Multiplication is done modulo 26, and the resulting products are replaced by their corresponding letters to arrive at the encrypted message.
Contributed by: Marc Brodie (January 2012)
Wheeling Jesuit University
Open content licensed under CC BY-NC-SA
Snapshots
Details
In order for an encrypted message to be decipherable, the encryption value must be a unit modulo 26, and in this case, the decryption value is its multiplicative inverse. Obviously, an encryption value of 1 is not used. Like the Caesar and other shift ciphers, the decimation cipher is a simple substitution cipher.
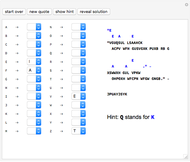
This Demonstration includes nine messages to illustrate decimation encryption. Selecting the decryption mode will give a random choice from a list of twelve messages distinct from the nine messages for encrypting. You can opt to decrypt an encrypted version of one of the nine original messages.
Cool spy lingo found at www.intelligencesearch.com/spy-codes.html.
Permanent Citation