JPEG Compression Algorithm

Requires a Wolfram Notebook System
Interact on desktop, mobile and cloud with the free Wolfram Player or other Wolfram Language products.
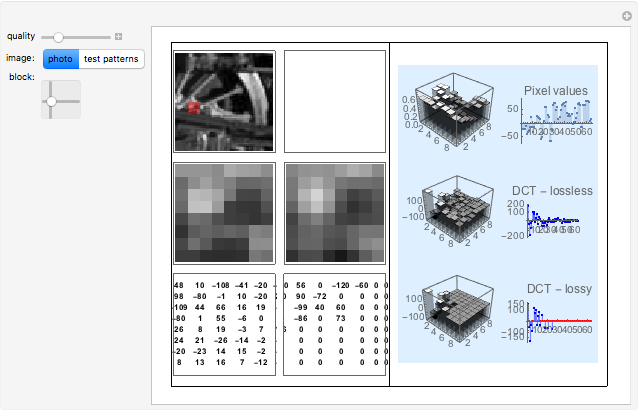
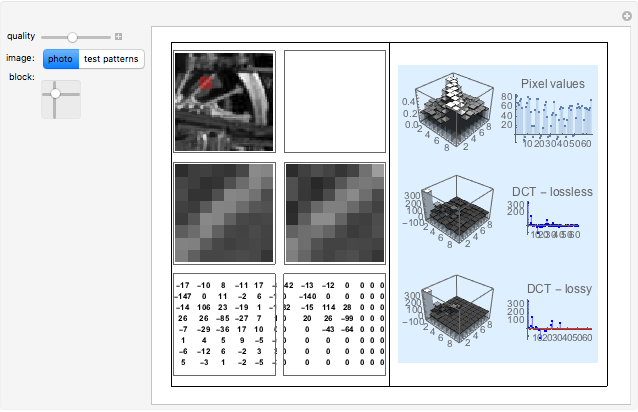
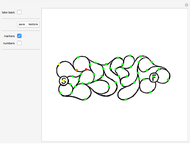
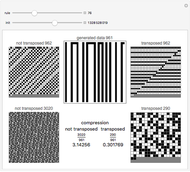
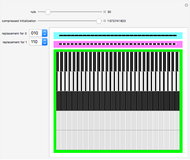
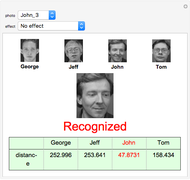
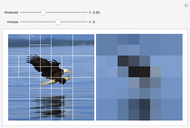
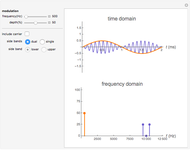
This Demonstration shows how a two-dimensional discrete cosine transform works on the image blocks during JPEG compression and how the data is degraded by the quantization matrix. Red points in the graphs on the right side display zeros, which are important for the file size reduction. More zeros give more size reduction but worse image quality. You can choose photos and images with patterns; most of them are difficult to compress by the JPEG algorithm.
Contributed by: Jakub Serych (May 2011)
Open content licensed under CC BY-NC-SA
Snapshots
Details
The JPEG compression algorithm (which is also used in MPEG compression) is based on the two-dimensional discrete cosine transform (DCT) applied to image blocks that are 8×8 pixels in size. DCT concentrates information about the pixels in the top-left corner of the 8×8 matrix so that the importance of information in the direction of the bottom-right corner decreases. It is then possible to degrade the low information value coefficients by dividing and multiplying them by the so-called quantization matrix. These operations are rounded to whole numbers, so the smallest values become zero and can be deleted to reduce the size of the JPEG.
In the columns from the left you can see: the original image, the chosen block and DCT coefficients matrix, the compressed image, the compressed chosen block and degraded block and its coefficient matrix, a 3D representation of pixels, the DCT coefficients and degraded coefficients and chosen block output—pixels, zigzag coefficients, and zigzag degraded coefficients.
Half of the sample photo is without any compression and the other half is already compressed by the JPEG algorithm. Can you recognize which half is which by eye? Can you recognize it by the coefficients?
References
[1] Wikipedia, "JPEG." (May 2011) http://en.wikipedia.org/wiki/Jpeg.
[2] International Communication Union, "Terminal Equipment and Protocols for Telematic Services," 1993, http://www.w3.org/Graphics/JPEG/itu-t81.pdf.
[3] J. D. Kornblum, "Using JPEG Quantization Tables to Identify Imagery Processed by Software," Digital Investigation 5, 2008 S21–S25, http://dfrws.org/2008/proceedings/p21-kornblum.pdf.
Permanent Citation
"JPEG Compression Algorithm"
http://demonstrations.wolfram.com/JPEGCompressionAlgorithm/
Wolfram Demonstrations Project
Published: May 6 2011