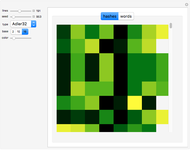
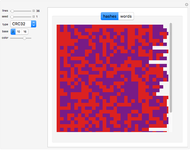
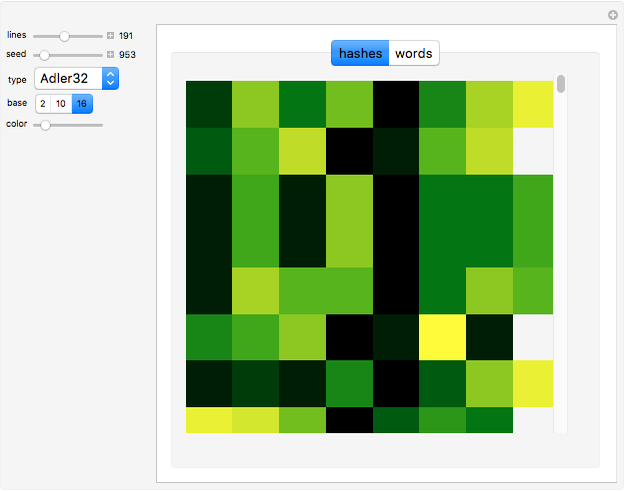
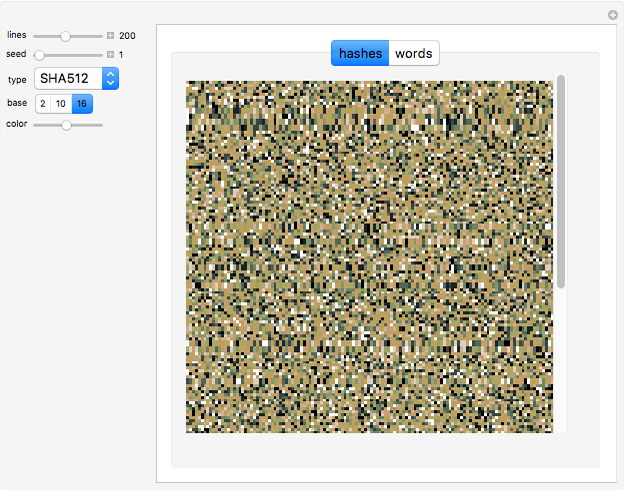
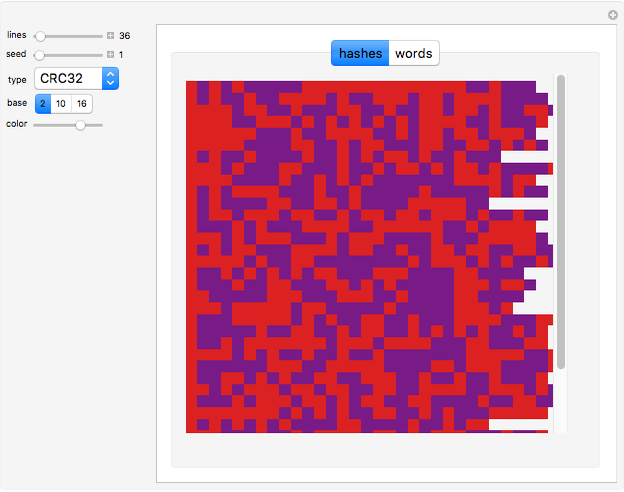
Hashing Words in Cryptography

Requires a Wolfram Notebook System
Interact on desktop, mobile and cloud with the free Wolfram Player or other Wolfram Language products.
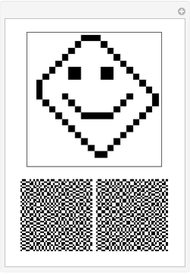
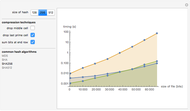
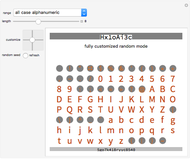
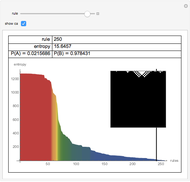
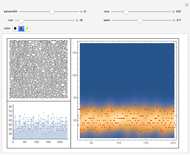
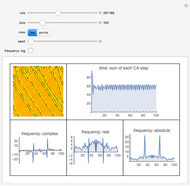
A cryptographic hash code is a one-way function that converts data to a sequence of obfuscated characters with a standard size (the message digest). The term "one-way" means the function is irreversible, i.e., it is not feasible to transform the encrypted information back into the original data.
[more]
Contributed by: Daniel de Souza Carvalho (August 2012)
Open content licensed under CC BY-NC-SA
Snapshots
Details
detailSectionParagraphPermanent Citation
"Hashing Words in Cryptography"
http://demonstrations.wolfram.com/HashingWordsInCryptography/
Wolfram Demonstrations Project
Published: August 16 2012