Fingerprints of Electronic Files: Performance Tests

Requires a Wolfram Notebook System
Interact on desktop, mobile and cloud with the free Wolfram Player or other Wolfram Language products.
Information stored in digital documents can be lost during transmission, migration, or when the storage medium breaks down or is corrupted. To ensure that the data has not changed, you can perform a digital fingerprint procedure. Up to a small margin of error, a digital fingerprint is unique to each document and therefore verifies the integrity (unaltered state) of the document.
[more]
Contributed by: Daniel Arndt Alves (March 2011)
Open content licensed under CC BY-NC-SA
Snapshots
Details
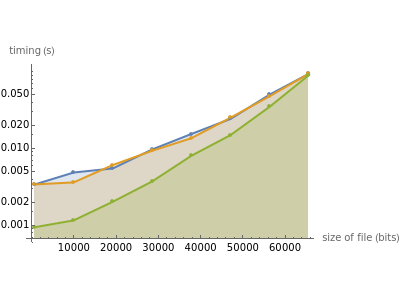
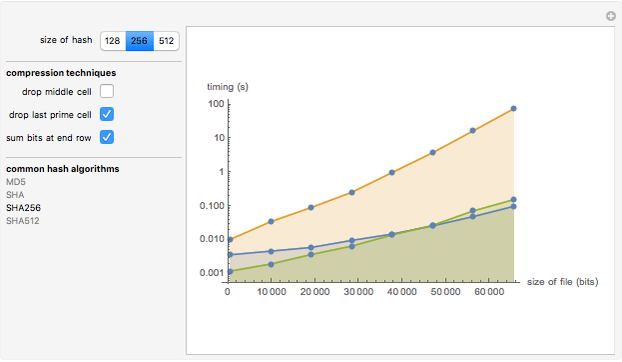
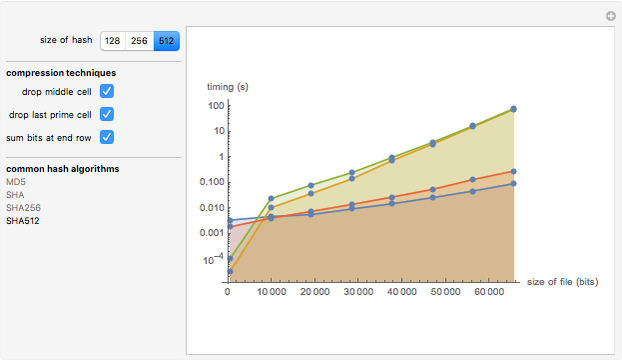
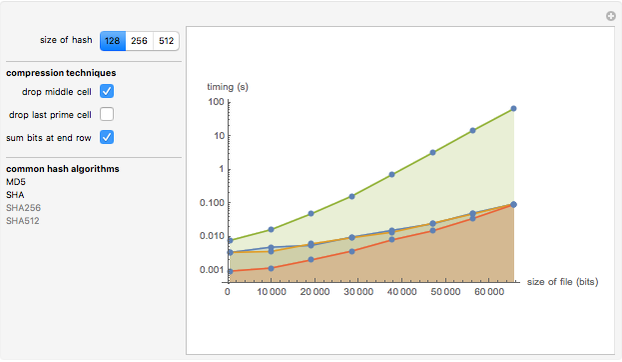
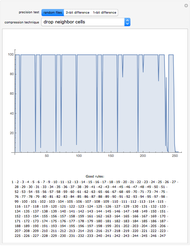
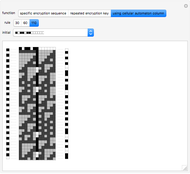
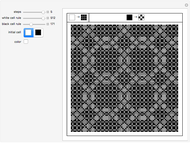
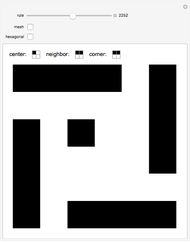
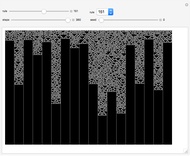
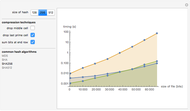
At every step, a cellular automaton rule is applied to the current state, and cells are dropped according to the compression technique being used.
This Demonstration presents some results of precision tests on research about finding an NKS way to generate fingerprints of electronic documents based on their contents, using the binary data of a document with an initial state and the result of computation as a fingerprint of this document.
More information about Document Management Systems: Wikipedia.
More information about Fingerprint Algorithms: Wikipedia.
This Demonstration was created during the New Kind of Science Summer School 2008 (NKS|Online) in Burlington, Vermont.
Permanent Citation
"Fingerprints of Electronic Files: Performance Tests"
http://demonstrations.wolfram.com/FingerprintsOfElectronicFilesPerformanceTests/
Wolfram Demonstrations Project
Published: March 7 2011