Hackers Language

Requires a Wolfram Notebook System
Interact on desktop, mobile and cloud with the free Wolfram Player or other Wolfram Language products.
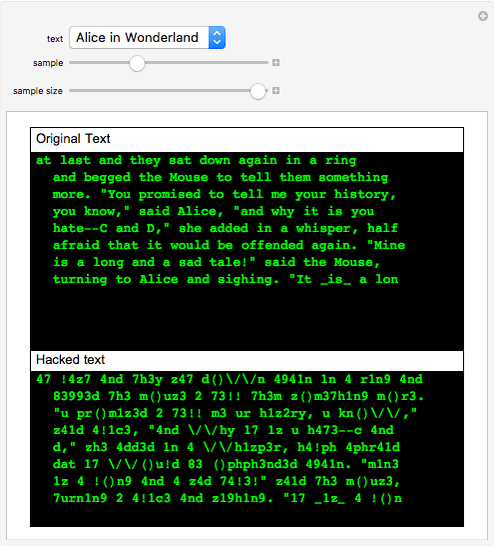
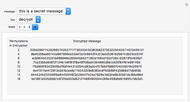
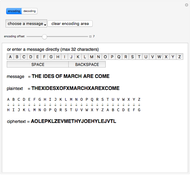
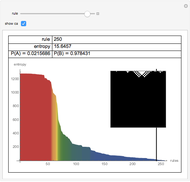
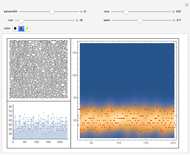
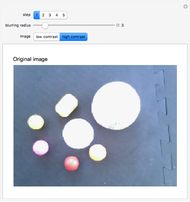
Criminal hackers usually leave messages when breaking into a website or any system. The messages are written in a kind of code. It is not meant to be cryptography; the idea is just to show that it was left by a hacker. The language replaces some characters, for example: t to 7, B to 8, l to 1, i to !, s to z, and so on, but there is no strong rule. There are also legal hackers who program free software and open source projects such as Linux Kernel, KDE and Gnome user interfaces, Apache web server, and many others.
Contributed by: Daniel de Souza Carvalho (March 2011)
Open content licensed under CC BY-NC-SA
Snapshots
Details
detailSectionParagraphPermanent Citation
"Hackers Language"
http://demonstrations.wolfram.com/HackersLanguage/
Wolfram Demonstrations Project
Published: March 7 2011